8 EASY WAYS TO HIDE YOUR IP ADDRESS FROM INTRUDERS
The “IP” in an IP address refers to the Internet Protocol. The “address” element refers to a unique number. This number associates with all of your online activities. It is very similar to the return address on a letter.
IP addresses are sets of numbers issued to computers, routers, websites and many more. It functions similarly to a conventional address. They pinpoint the location of every device or system in the network anywhere on the planet. The TCP/IP Protocol uses them to let devices communicate among themselves.

There are numerous reasons to be anonymous online. IP addresses can determine your physical location. They can do so with surprising accuracy in some cases. Advertisers and adversaries can track you online using these addresses. This can reveal your personal identifiers like phone numbers. They can also enable others against you to launch targeted attacks.
You could even be fleeing an overbearing or tyrannical government. When reporting in unsafe places or on sensitive issues, journalists are more prone to disguise their IP addresses. Hence, it is important for people to be aware of how to hide IP address. This way they can keep themselves safe in the event that they need to.
In this blog, you will find the easiest and most affordable ways of IP address hiding.
Table of Contents
Use a Virtual Private Network (VPN). 1
Connect to a different network. 3
Renewing your IP address on Windows: 3
Renewing your IP address on Mac: 4
Use a Virtual Private Network (VPN)
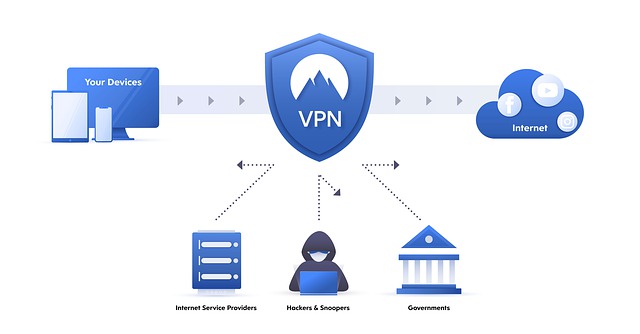
When you visit a website with your browser, a request leaves your device. It travels to the website’s server and returns with the information you requested. Along the route, attackers, nosy government agencies and others might intercept it. They can then trade location and other essential identifying information.
A virtual private network, or VPN, is the best IP address hiding technique. It adds another layer to this equation. Instead of directly accessing a website’s servers, the VPN establishes an encrypted tunnel. This tunnel runs between you and the VPN service’s server. This tunnel then connects to the public internet and retrieves the needed information. This information returns to your computer via the tunnel. Hence, it guarantees that no one can intercept your web traffic. If they do, the observer will see the VPN’s IP address rather than yours.

The top VPN services go further. Alongside being an efficient IP address hider, they include extra features like ad blocking and virus prevention. Static IP addresses are even available for purchase from some VPNs, such as TorGuard. They are different from the address that your ISP or VPN connection provides. This is a permanent address that is normally limited to a specific country.
VPNs provide an extra step to your web browsing. This would usually results in a slower experience. However, top-tier VPN providers, on the other hand, will only slow you down minimally. You might not even notice the difference if your connection is strong enough.
Here is a list of the best VPNs that are available in today’s market.
Use a Proxy
A proxy server works as an intermediary between your computer and the internet. It becomes a middleman between a client and a network of clients. It then transmits requests and receives and delivers responses from servers. If you want to use a proxy, you may need to manually update your device’s proxy settings.
Some proxy servers can substitute a fictitious IP address for yours. You will appear to be from the same country as the proxy server. If you are using a proxy service to hide IP address, keep in mind that not all proxies are offer equal features.

Transparent proxies cannot hide IP address or the fact that you are using a proxy. Anonymous proxies are good for IP address hiding but not your proxy usage. High anonymity (or elite) proxies are efficient in IP address hiding and your proxy usage both.
If you’re trying to access media through a proxy, be aware that some sites or content platforms may block traffic from recognized proxies.
Most proxies, unlike VPNs, do not encrypt your traffic or hide your IP address from intercepting on its journey from your device to the proxy. Hence, VPNs are more dependable than proxy servers, especially free web-based proxies. As a result, proxies are most useful as a short-term solution to hide IP address rather than a long-term privacy strategy.
Click here to find the best proxy services available.
Use Tor
Even if you use a VPN, your data travels in a more or less direct channel between your computer and the Internet. Making your trip more roundabout, however, obviously obscures your IP address. You also make it much more difficult to find yourself.
Tor stands for The Onion Router. It uses a network of computers spread throughout the globe. It can hide IP address and make your digital trail more difficult to track. Your computer sends out layered requests in place of a single request from your house to the website’s server and back. Each of these requests undergoes encryption separately. Then you set out on a route from Tor node to Tor node until you exit the network and arrive at your destination.

Even if someone intercepted your transmission between nodes, there are layers of encryption. They ensure that they would not be able to determine where the chain started or ended. Theoretically, to figure out who you are, the attacker has to map your complete trip via the Tor network.
Of course, not everything in the real world works flawlessly. But, Tor is open about its flaws and actively tries to improve the network.
Tor is most commonly connected with secretive and shady Dark Web sites. Nevertheless, it is one of the best IP address hider tools available. It is of use on a daily basis by persons concerned about their safety. People wishing to bypass the limits of oppressive government censorship also find this essential. It is also completely free.
Use a NAT Firewall
NAT stands for Network Address Translation. A NAT firewall, allows many devices on the same network to share the same public IP address. However, they still have separate private IP addresses. Individual device requests and data reach their destination using the router’s public IP address via NAT. This saves address space (the amount of IP addresses accessible). This is helpful for avoiding unwanted inbound contact with potentially harmful computers online.
A NAT firewall is capable of private IP address hiding rather than your public IP address. All devices connected to a NAT-enabled router will share a single public IP address. It will block any online communication not in response to a request you sent from a private IP address. They lack a private IP address to which they can forward it. As a result, the firewall deletes all other requests and data packets.
Connect to a different network
Your IP address changes whenever you switch networks. If you believe someone is hacking or tracking your IP address, you can switch networks to obtain a new one.
You can utilize your phone’s mobile data connection. You can also connect to a public or private Wi-Fi network. However, keep in mind that open networks and public Wi-Fi hotspots can be a haven for hackers. They are waiting to take advantage of the absence of encryption and authentication. So, if at all possible, choose networks that require a password.
Ask your ISP
Your Internet Service Provider (ISP) is in charge of allocating IP addresses. So, if you need to change it to hide this IP address, call them. You will require your account details, as well as your current IP address for this.
It should not be too difficult to obtain a new IP address, but don’t expect it to remain the same indefinitely. This is going to be a dynamic IP address. Your IP address may most likely vary from time to time. This is due to the regular recycling of IP addresses. This is in order to maintain the limited amount of available IP addresses.
You could request a permanent static IP address too. However, there may be an application process and an additional price.
Renew your IP address
If you link to an internet router via Wi-Fi or ethernet cable, you will mostly have a private IP address. While it isn’t as important to hide this IP address while online, there may be times when you need to change it.
Do the following in your Windows Command Prompt or Mac Terminal to accomplish this.
Renewing your IP address on Windows:
- Open Command Prompt. Run it as administrator.
-
Type in the following command:
ipconfig /release
ipconfig /renew
- A new local IP address should now appear.
Renewing your IP address on Mac:
- Open System Preferences from the Apple menu.
- Choose a network.
- In the left pane, highlight the network to which you’re connected.
- Select Advanced…
- Choose the TCP/IP tab.
- Select Renew DHCP Lease.
- Your Mac’s private IP address will now change.
Unplug your modem
This is not guaranteed to work. However, disconnecting and replugging your internet modem can often result in a new IP address. Your old IP address gets recycled if you lose contact with your ISP. You will then get a new IP address when you re-establish a connection.

The longer you leave the modem disconnected, the better your chances of success. So if you have to, try unplugging it for the night.
For this to work, your ISP must employ dynamic IP addresses.
It is impossible to hide your IP address from everyone. However, you can be able to obtain a decent level of anonymity for everyday purposes. Your VPN provider is the only company that can link your online behavior to your IP address when you use one. This is why it is critical to select a VPN service that has a solid reputation for security. It must never retain logs of user activities.
Your ISP will be able to view the type, timing, and amount of traffic you transmit to the VPN server. However, the details of your activity remain secret. Tor also works in a similar fashion. Many proxies don’t encrypt your traffic. This means that your ISP will be able to see what you are doing even if you are using one. All websites and services you access when connected to a VPN will see the VPN’s IP address rather than yours.
The main goal of hiding IP address is to keep third-party observers out of your online activities and location. Such third party entities include websites, marketers who employ ad-tracking tactics, and cybercriminals. It is critical to be proactive when your safety and privacy are at stake.